This is your guide for hacking beginners. This post you will Learn to hack and i will shows you 2 hacking strategies:
- If you are interested in computers and technology, go through the entire tutorial step-by-step.
- If you’re less technical, skip ahead to the Social Engineering chapter for an introduction to non-technical hacking.
Learn hacking beginner FAQ
Why should I learn hacking?
Many legal reasons motivate hackers worldwide to engage in hacking. because
- You can have a lot of fun hacking.
- You can hack yourself if you forgot your password.
- You want to build up a second income (or full-time job).
- You want to understand computers better.
- You use software that has locked you out (database).
- You want to know the hacking strategies to protect yourself from a hack.
- You want to do something good for society.
Is hacking illegal?
You are allowed to hack if you hack your own systems or support other organizations or people to close their vulnerabilities ( ethical hacking ). You need a written declaration with the scope of the hack and the signature of the other person that you are allowed to hack (verifiability).
Any form of self-enrichment, causing damage, violation of privacy and data theft are prohibited
Do I need prior knowledge?
No, you do n’t need any previous knowledge for this guide .
A broad prior knowledge or an IT degree will help you to sort through new learned hacking topics faster. A non-specialist without IT knowledge can try the social engineering strategies in the first step and later immerse themselves in the IT topics.
You can work through the tutorial faster if you enjoy working with technology and computers. Hacking beginners benefit from perseverance , advanced Google skills , reading comprehension and lots of creativity.
Do I need to be able to program?
No, programming helps you understand hacking tools more easily.
Programming is not a must for the beginners . For the advanced topics, you should familiarize yourself with the basics of a programming language.
What computers do I need for hacking?
You don’t need a fast and powerful computer to hack. Windows, Linux and macOS are good for hacking. Kali Linux is suitable as a hacking environment . we have made a list of best laptop for hacking you may check it to get a new one if needed.
Most hacking software is “pre-installed” or available for free (open source). A few professional hacking tools cost a lot of money that the well-paid ethical hacking professionals use. The internet provides an open source alternative in most cases .
Hacker Types – The Motivators
Black Hat Hacker – Illegal and Criminal
Black hats are considered the pizza-eating computer zombies. They sit in Mom’s basement and blackmail companies like Amazon, PayPal and Google, steal money and or cause damage. Black hats operate illegally and end up in prison.
White Hat Hacker – Legal + Profitable
White hats enjoy hacking websites , apps , and programs. They help companies and people find all sorts of errors, vulnerabilities and bugs in their software.
Gray Hat Hackers – Danger for companies
Gray hats (un)intentionally publish the vulnerabilities they have found in known operating systems and software on the Internet. The black hats can exploit the vulnerabilities. The companies need to close the vulnerability quickly to reduce the risk of a black hats hack.
Script Kiddies – Big Mouth and Dangerous
The 13-year-old Script kids find a hacking tool on the internet. The minors attack companies or a private individual and deliberately infuriate their victims.
Parents are responsible for the damage caused by their child.
Professionals and penetration testers
If you are looking for a meaningful job with a good salary, work in the IT security department of a company. Alternatively, you can earn your money as a freelancer with the bug bounties .
Blue Team / Red Team training
The IT security analysts (protection = Blue Team) protect your systems against attacks by the ethical hacker group (attack = Red Team). In the competitions, the Blue Team protects a server with demo data from the hackers. The hackers try to penetrate the system unnoticed.
Your guide in 10 steps from 0 to hacker
These 10 steps should get you started on hacking. Step by step!
Get inspired by the hacking stories
Some news websites and bloggers report on the interesting hacks that have taken place in the past.
Todo: Read through 3+ inspirational hacking stories. You will surely be surprised how easy hacking is. The hackers use unconventional tricks to trick companies, paralyze computers and exercise power over institutions. The stories inspire you to start hacking and give you an idea of what this super ability can do:
- Hacker Capitan Crunch made free domestic and international phone calls through AT&T by generating a 2,600 hertz tone through a toy whistle (1969).
- The Conhive crypto trojan generated bitcoins using the power of the computers that visited a Coinhive infected website. This Trojan is a real money printing machine.
- The Morris virus paralyzes a large part of the UR Internet. 6000 computers fail and the hacker has to pay a $10,000 fine (1988).
- Criminals steal the documents from NASA about the Mars mission (2019).
When reading the stories I have to smile about the old errors and bugs in software .
The bloggers describe the hacks clearly and with the necessary drama because the hacks could have ended more seriously.
The stories should motivate you to see hacking as something worth striving for. You get to know the power through the hacking stories that a hacker can exert on the companies and institutions.
First successful hacking attempt
Second, try hacking beginner tutorials .
Todo: Hack your own systems. Alternatively, the Internet makes public demo hacking systems available to give you a first impression of the activity.
- Damn Vulnerable Web Application (DVWA): A test website with many errors and bugs that you can exploit. This is a real playground for hackers.
- Hack the box: Test your skills on realistic servers.
You can acquire the technical knowledge for this in the next steps. My hacking tutorials are tailored to a specific case. The tutorials guarantee your success if you follow the instructions exactly.
In reality, the professionals hack according to the trail-and-error principle and prior information gathering.
Establish your focus
You can start hacking in many different areas, All hacking areas are closely intertwined. You can reuse what you’ve already learned in another hacking section. At the beginning you should not bring up too many topics. Set a focus so that you can achieve initial success.
Understand technical basics
The following section gives you a wide selection of topics from the field of the web.
Some of the technical basics will help you better understand the hacking software. You will overlap with other areas, e.g. B. Networks and Android notice. The list below is expandable with other topics.
Todo: Learn about the basics of your hacking rubric.
You don’t need to learn all the basics at once to hack. The more you know, the more tools you have to hack successfully. For a successful hack, deepening in just 1 basic topic is sufficient, so that you can hack into someone else’s system.
The hacking/programming world uses a lot of technical words and jargon that you will learn over time.
- The Internet: OSI model, routing, packets, frames, Ethernet, IP addresses, TCP, UDP , various protocols such as HTTPs , HTTP, FTP, Telnet, SSH, etc.
- Anonymity on the Internet: Virtual Private Network (VPN) , The Onion Router (TOR), Cookies, Fingerprinting, WhosIP, Backtracing
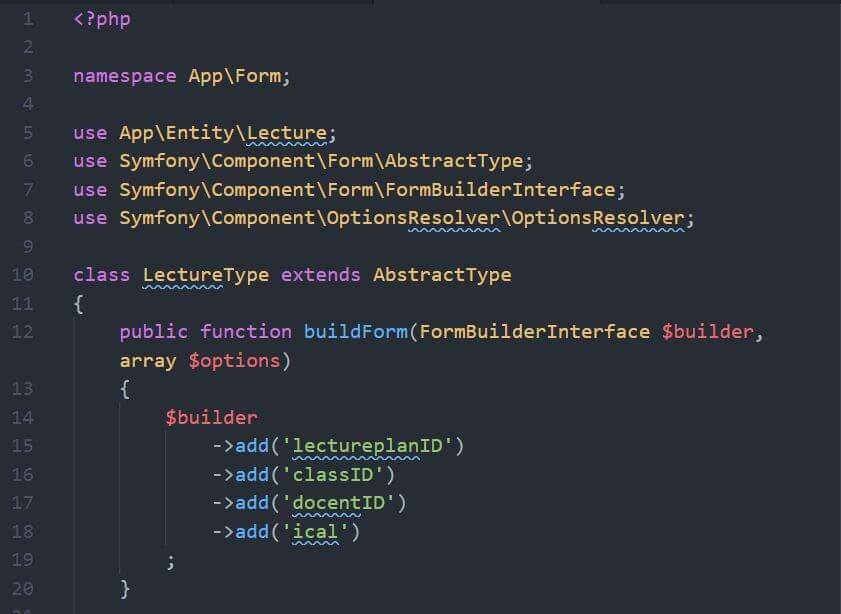
- Designing a website: Basics of HTML, CSS and JavaScript / TypeScript, JavaScript Trojans , Bitcoin miners
- Web: ports, sessions, tokens, request methods, internet encryption, browser engines
- Legacy and Modern Databases: Database Types , Transaction, Access, Table, Column, Record, SQL, NoSQL
- Legacy and modern architectures: 3-tier architecture , REST-API, Graph-QL, microservices
- I recommend online lectures: software architecture, operating systems and networks (communication systems).
- (optional: A proper programming language like Java, Apple’s Swift, C family, Python, Ruby, etc…)
Master hacking basics
Before you start hacking other people’s systems, you should be aware of the applicable law . With well-intentioned hacking, you can quickly make yourself liable to prosecution if you cross a boundary such as privacy.
Todo: Hack your own systems first. Below I list the most important hacking topics, which you can delve into step-by-step.

- OWASP Top 10 : The Open Web Application Security Project (OWASP) aims to make tomorrow’s digital world more secure. The TOP 10 show you the most common mistakes made by developers.
Understand all 10 vulnerabilities. The probability that you will find a top 10 bug is high.
An efficient hacker uses the OWASP Top 10. In 20% of the search time you will find 80% of the vulnerabilities (Paetro principle). - Bugs in software: Why do errors occur in the software? How do companies prevent the hacking loopholes? How can I discover software errors? Is there a bug-free software? Find out about good software quality and the bug bounty programs .
- Social Engineering: If you’re not that technical and have good speaking and acting skills, try social engineering. The tricks of non-technical hacking put you on a different path to hacking success. Read the Social Engineering section if the topic interests you.
- Hacking procedures: Deal with the essential attacks, methods and procedures for hacking such as B. a buffer overflow, attacks on encryption , reverse engineering or brute force . Every hacker should know these guys.
- Malware types: Malware comes in different forms: (polymorphic) viruses, keyloggers, rootkits, RAT, trojans, worms and adware. Each malware type has a different goal.
- Vulnerabilities: Hackers love vulnerabilities. The IT professionals penetrate other systems without much effort or hacking skills. The Common Vulnerabilities and Exposures (CVE) are software (and hardware) bugs. MITER should only list the CVEs that companies can optimally update (patch). The CVSSv3 vector indicates the severity of a vulnerability. 10 is the maximum.
Switch to Kali Linux
Todo: Install Kali Linux on a virtual machine , a separate hard drive or partition.

Kali-Linux is a Linux system that comes with many hacking tools right from the start . You can start hacking without looking for the programs/tools and tearing your hair out at the installation procedures.
Advice on the software: Focus on how the hacking tools work, how to use them correctly and how to set them up.
- Linux basics: Find out about the following topics: the differences to Windows, macOS and other operating systems, advantages and disadvantages of Linux systems, rough structure and function of UNIX.
- Basics Bash: Like Windows (CMD, PowerShell ), Linux has a console. Sooner or later you will love the freedom of the console. Learn the basics of the console to be able to use many hacking tools more easily.
When intruding into foreign systems, you can rarely use a graphical interface. With 11 words (commands) you can carry out 80% of the most important actions in the console.
Find out about the bug bounty programs
To keep hacking from losing its appeal, you should sign up for a bug bounty program.
Some tech companies such as Microsoft, Apple and other large IT companies give the hackers a nice sum (up to USD 1,000,000) if they professionally point out the vulnerabilities to the company.
The HackerOne website provides a platform where small and large businesses offer bug bounties. Sign up today for free. I explain how you can earn money with HackerOne in the bug bounty tutorial .
Learn to Hack – Manual Steps
Todo: Start manual hacking.
The website “Hack This Site” is suitable as a hacking playground.
The website remains unprotected against the most popular hacking strategies so that new hackers can learn the basics in practice. Start with the following strategies:
- Enter an XXS script in an input field and wait for the response.
- Test an SQL injection to bypass a password-protected login .
- Use the default password lists to hijack the admin account.
- Start by gathering information about the target (server type, operating system, framework, operator, location, known CVEs) to get an overview of the target.
The following websites offer some tutorial and hacking sandboxes where you can let off steam:
- DefendThis : An interactive hacking platform
- Hack.me : One-button hacking website (without going illegal)
- Juice Shop : Hack a Juice Shop web shop locally on your computer
Automatic Hacking + Scanning Tools
Know some of the basics mentioned in Steps 4 and 5 before reading on. Learn the basics for a specific hacking tool before using a hacking program.
- How does the tool work?
- What do the manual commands in the console look like?
- What can I achieve with the program?
- Where are the challenges?
- When and why does this hack work?
The script kiddies skip all the basics, don’t know the legal situation . The parents can (in the very worst case) be sued to imprisonment and the children committed to a psychiatric ward.
Here is a list of the well-known hacking tools :
- Burp : Vulnerability scanners and manual web hacking tools
- Nmap (Zenmap): Network scanning tool for network admins
- Nessus : Tenable’s vulnerability scanner
- Wireshark : network recordings and packet analysis
- HTTPrint : recognition software for frameworks, servers and co.
- Metasploit : Penetration testing platform with vulnerabilities
- OpenVAS : Open source vulnerability scanner
- SQLmap : SQL injection tester with an automatic
- AirCrack : Crack W-LAN or test a W-LAN for security
- … and other top hacking tools
Keep going every day
A good hacker never stops learning . Every day the hacker learns new hacking methods, tries out trends and plays around with the terminal console.

The hacker MUST learn new things because hacking is expanding every day. Many new vulnerabilities, protections, and hacks appear on the Internet every day.
Social engineering – learn to hack
Social engineering is based on psychological tricks. The idea of social engineering is to exploit the human vulnerability. You try to manipulate people to get passwords or access.
With the psychological tricks and theatrical skills, the hackers can get almost any password. Criminals can bypass IT security spears and access confidential information.
How to become a successful hacker
What makes a good hacker? This section is intended to teach you which soft skills you should pay attention to as a hacker. You should memorize the following habits from the start.
- Doesn’t give up easily and doesn’t expect quick success. If a hack doesn’t work, he looks for a new approach. If he doesn’t understand a technology, he proactively asks someone else.
- Gets to know new hacking strategies every day. If the hacker stops technologically, then he will fail more often in the future. A good hacker is always up to date, educates himself, socializes.
- Finds out about the latest vulnerabilities in computer software/hardware (CVEs).
- Works together with other hackers and programmers. A hacker should not be a loner. The hacking spaces , conferences and meetings offer the hacker the ideal platform for new ideas.
- Takes a strategic approach and tries to improve and adapt its processes with automated tools . Before he uses a tool, he thinks carefully about which one is the right one. You don’t use a hammer on a screw!
- Specializes in one area of hacking and goes deep into the subject. Superficial learning will not get you there as quickly as diving deep into a lesson.
- Takes breaks (with Pomodoros and after 8 hours it’s over). Love it man not to hack. You should only be able to get started with full motivation and zest for action during the hacking period.

I love this knowledge so much God blessing
I want to be haker
Muito bom