acccheck Package Description
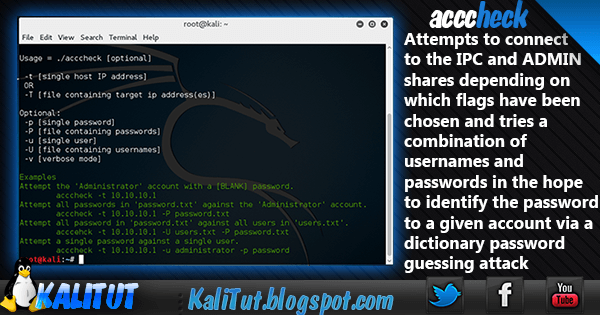
Acccheck Attempts to connect to the IPC and ADMIN shares depending on which flags have been chosen, and tries a combination of usernames and passwords in the hope to identify the password to a given account via a dictionary password guessing attack. this tool is designed as a password dictionary attack tool that targets windows authentication via the SMB protocol. It is really a wrapper script around the ‘smbclient’ binary, and as a result is dependent on it for its execution. only use -v mode on very small dictionaries, otherwise, this has the affect of slowing the scan down to the rate the system writes to standard out.
he Server Message Block (SMB) Protocol is a network file sharing protocol, and as implemented in Microsoft Windows is known as Microsoft SMB Protocol. The set of message packets that defines a particular version of the protocol is called a dialect. The Common Internet File System (CIFS) Protocol is a dialect of SMB. Both SMB and CIFS are also available on VMS, several versions of Unix, and other operating systems.
Most usage of SMB involves computers running Microsoft Windows, where it was known as “Microsoft Windows Network” before the subsequent introduction of Active Directory. Corresponding Windows services are LAN Manager Server (for the server component) and LAN Manager Workstation (for the client component)
SMB can run on top of the Session (and lower) network layers in several ways:
Directly over TCP, port 445;
Via the NetBIOS API, which in turn can run on several transports;
On UDP ports 137, 138 & TCP ports 137, 139 (NetBIOS over TCP/IP);
On several legacy protocols such as NBF (incorrectly referred to as NetBEUI).
The SMB “Inter-Process Communication” (IPC) system provides named pipes and was one of the first inter-process mechanisms commonly available to programmers that provides a means for services to inherit the authentication carried out when a client first connected to an SMB server.
The simplest way to run acccheck is as follows:
./acccheck.pl -t 10.10.10.1
This mode of execution attempts to connect to the target ADMIN share with the username ‘Administrator’ and a [BLANK] for the password.
./acccheck.pl -t 10.10.10.1 -u test -p test
This mode of execution attempts to connect to the target IPC share with the username ‘test’ and a password ‘test’.
Each -t, -u and -p flags can be substituted by -T, -U and -P, where each represents an input file rather than a single input from standard in.
example
./acccheck.pl -T iplist -U userfile -P passwordfile
Only use -v mode on very small dictionaries, otherwise, this has the affect of slowing the scan down to the rate the system writes to standard out.
Any username/password combinations found are written to a file called ‘cracked’ in the working directory.
- Options:
- -t [single host IP address]
- -T [file containing target ip address(es)]
- Optional:
- -p [single password]
- -P [file containing passwords]
- -u [single user]
- -U [file containing usernames]
- -v [verbose mode]
How to use acccheck
- Attempt the ‘Administrator’ account with a [BLANK] password.
acccheck.pl -t 10.10.10.1 - Attempt all passwords in ‘password.txt’ against the ‘Administrator’ account.
acccheck.pl -t 10.10.10.1 -P password.txt - Attempt all password in ‘password.txt’ against all users in ‘users.txt’.
acccehck.pl -t 10.10.10.1 -U users.txt -P password.txt - Attempt a single password against a single user.
acccheck.pl -t 10.10.10.1 -u administrator -p password

Leave a Reply